Have you ever clicked a link and wondered if it was safe? Or heard about a big data leak and thought, “Could that happen to me?” It usually starts with something called a vulnerability. That’s a simple term for a cybersecurity weakness in a system, like a crack in a wall that someone can sneak through.
Attackers look for these cracks all the time. And if they find one, they can get into systems, steal data, or cause major damage. Sounds serious, right? Don’t worry, we’re breaking it down in simple terms, so you know what cybersecurity vulnerabilities are and why they matter.
What Are Cybersecurity Vulnerabilities?
The definition of a cybersecurity vulnerability is a weakness or a flaw in a system, network, or software that can be used by an attacker. Security vulnerabilities can open the door for attackers to gain unauthorised access, steal sensitive data, or disrupt operations.
A few recent metrics show why vulnerabilities are not just a technical detail.
|
Metric |
Value |
Period |
|
Exploit vulnerability as a way to breach |
+180% YoY |
DBIR 2024 vs DBIR 2023 |
|
Ransomware or extortion in breaches |
32% |
Data for 2023 (reported in 2024) |
|
Human element in breaches |
68% |
Data for 2023 (reported in 2024) |
|
Supply chain interconnection |
15% (was 9%) |
YoY change (reported in 2024) |
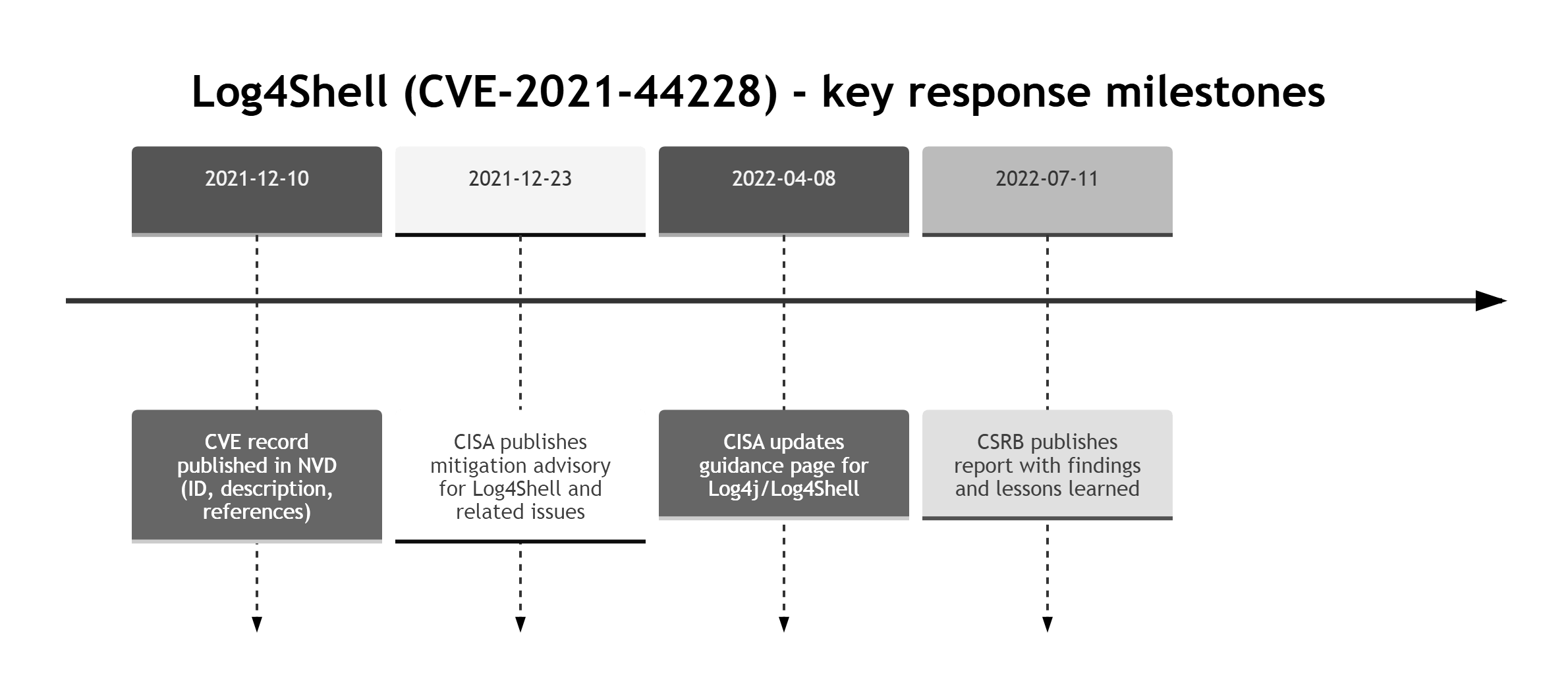
A well-known case is the Log4Shell vulnerability (CVE-2021-44228), where attackers exploited a flaw in the Log4j logging library to enable remote code execution on affected servers worldwide. This single flaw impacted major platforms and triggered global emergency patching.
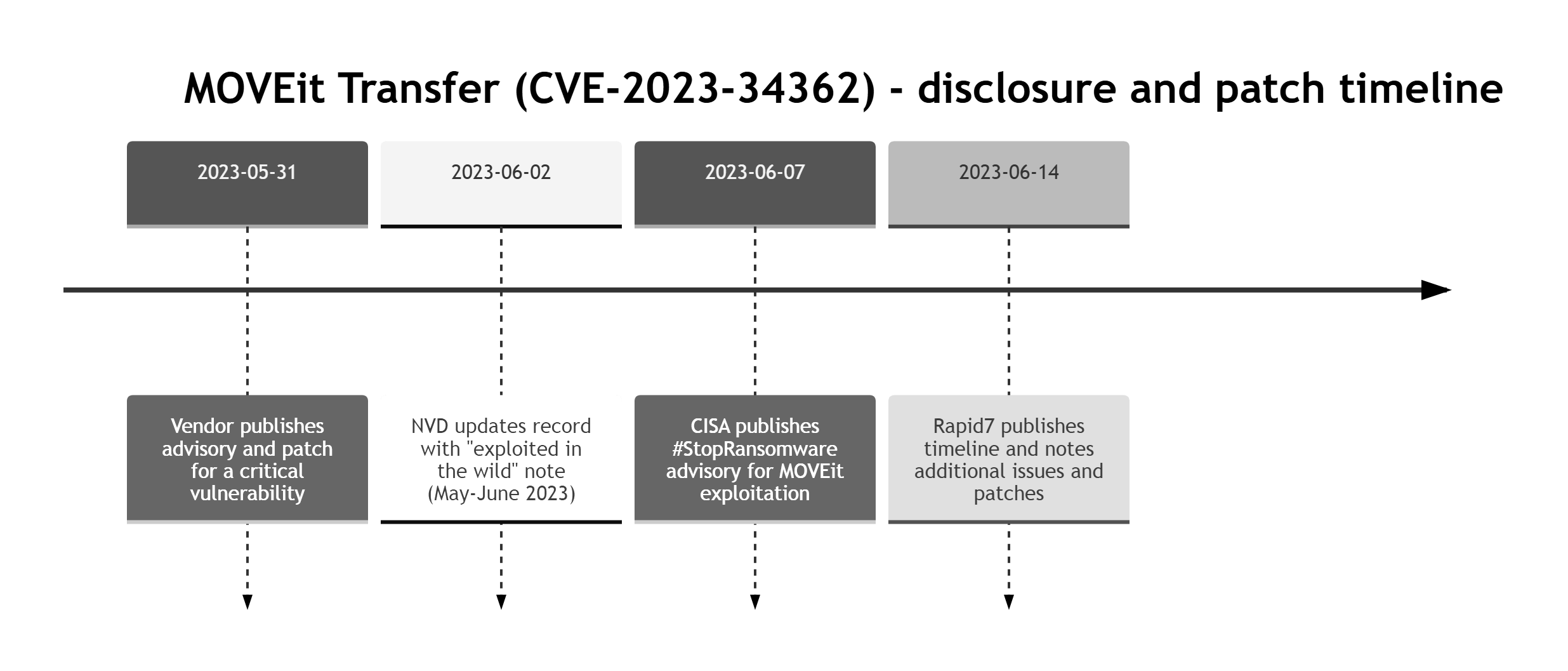
Not all vulnerabilities stem from code. In 2023, the MOVEit file transfer breach exposed data from governments and large corporations after attackers exploited a vulnerability in MOVEit Transfer. The attackers exploited this gap to steal vast amounts of information from secure environments.
What Is the Difference Between a Threat, Vulnerability, and Exploit?
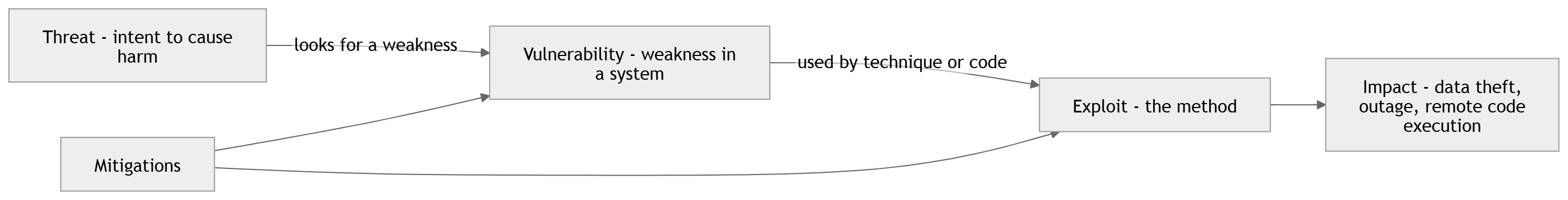
The terms threat, vulnerability, and exploit are sometimes used interchangeably in vulnerability management, but they mean different things; however, they have different implications:
- A threat is a potential cause of harm to systems or data.
- A vulnerability is a weakness in a system, application, or configuration that could be exploited.
- An exploit is a technique or code that takes advantage of a vulnerability.
We can understand these terms to have a better impression of how attacks occur and how they can be avoided. The definition of cybersecurity vulnerability is of particular concern. Without a vulnerability (or another weakness to abuse), many threats cannot be realized.
|
Term |
Meaning |
Example |
Role in Attack |
|
Threat |
A potential danger to data or systems |
Attacker trying to steal credit card data |
The motivation or intent |
|
Vulnerability |
A flaw or cybersecurity weakness in the system that can be targeted |
Unpatched software with a known security bug |
The opening or doorway |
|
Exploit |
The method used to abuse the vulnerability |
Code or a technique used to trigger the weakness (for example, an SQL injection payload) |
The weapon or technique used |
If you want a quick mental model, use this simple chain.
What Are the Common Types of Cyber Vulnerabilities?
Even minor flaws can become dangerous when they are exposed and reachable. Attackers look for weaknesses - vulnerabilities - when planning an attack. Cybersecurity vulnerabilities can cause serious damage when they are detected late. Avoid such damages by getting to know some of the security bug types in cybersecurity and address them early.
Table: Five common vulnerability types: examples, how they are found, and how they are usually fixed.
|
Vulnerability type |
Example |
How it is usually found |
How it is usually fixed |
Quick check |
|
Software |
Outdated library or component |
SCA, vulnerability scanner, SBOM review |
Patch or upgrade, temporary mitigation |
Do we have an update SLA? |
|
Network |
Admin port exposed to the internet |
Port scanning, EASM, firewall audit |
Close port, VPN or Zero Trust access, segmentation |
Which ports are publicly reachable? |
|
Human |
Phishing or weak password |
Phishing simulations, email telemetry, IAM reports |
MFA, training, block legacy auth |
Is MFA enabled everywhere? |
|
Hardware |
Vulnerable device firmware |
Asset inventory, vendor advisories |
Firmware updates, replacement, isolation |
Which devices are missing updates? |
|
Misconfiguration |
Public bucket or overly broad permissions |
CSPM, IaC scanning, config reviews |
Fix policies, guardrails, least privilege |
Do configs get checked before prod? |
Software Vulnerabilities in Cybersecurity
They are defects or bugs in programs and applications. At times, an application is issued with programming errors or even program flaws that are not spotted. When they are not corrected promptly via updates or patches, attackers can exploit them.
As an example, there could be a security loophole in your web browser or an operating system that the Attacker can use to install malicious software without your consent. This is one of the most common sources of security issues, and that is why frequent updates are necessary.
Vulnerability in Network Security
They occur when the networks that interlink your devices, such as routers, firewalls, or servers, fail to be secured. When these components of the network are wrongly managed or when they apply inefficient configurations, Attackers can infiltrate them and intercept or steal information.
A common issue is exposing unnecessary ports or management interfaces to the public internet. If a business fails to secure and monitor its network, it becomes an easier target for attackers.
Human-Related Vulnerabilities
It is not always a problem of technology; one must remember that people make mistakes as well. It involves making use of weak passwords, becoming a victim of phishing messages, or sharing sensitive information.
Even strong security controls can be undermined if someone clicks a malicious link or enters credentials into a fake login page. Such errors are so widespread and are commonly employed by attackers since they understand that people are often easier to deceive than systems.
Hardware Vulnerabilities
Not every threat is digital; there are those brought by physical devices. Occasionally, the hardware or software (known as firmware) of a device is defectively designed in a way that can be abused. As a small example, a security camera or smart home device may contain a built-in backdoor or insecure default settings that may allow Attackers to access everything in your network.
In case the machine has a default username and password that has not been changed, it becomes even simpler to breach the security and gain control over it.
Misconfigurations
It happens when systems are deployed in the wrong manner, either through ignorance or due to mistakes, lack of review, or missing guardrails. For example, making a private cloud storage folder publicly accessible can expose confidential documents to anyone on the internet.
It is quite unexpected that these mistakes are rather ordinary and are ignored until there is an attack that occurs. Sophisticated systems are not safe either unless they are configured properly and are well maintained through regular checks.
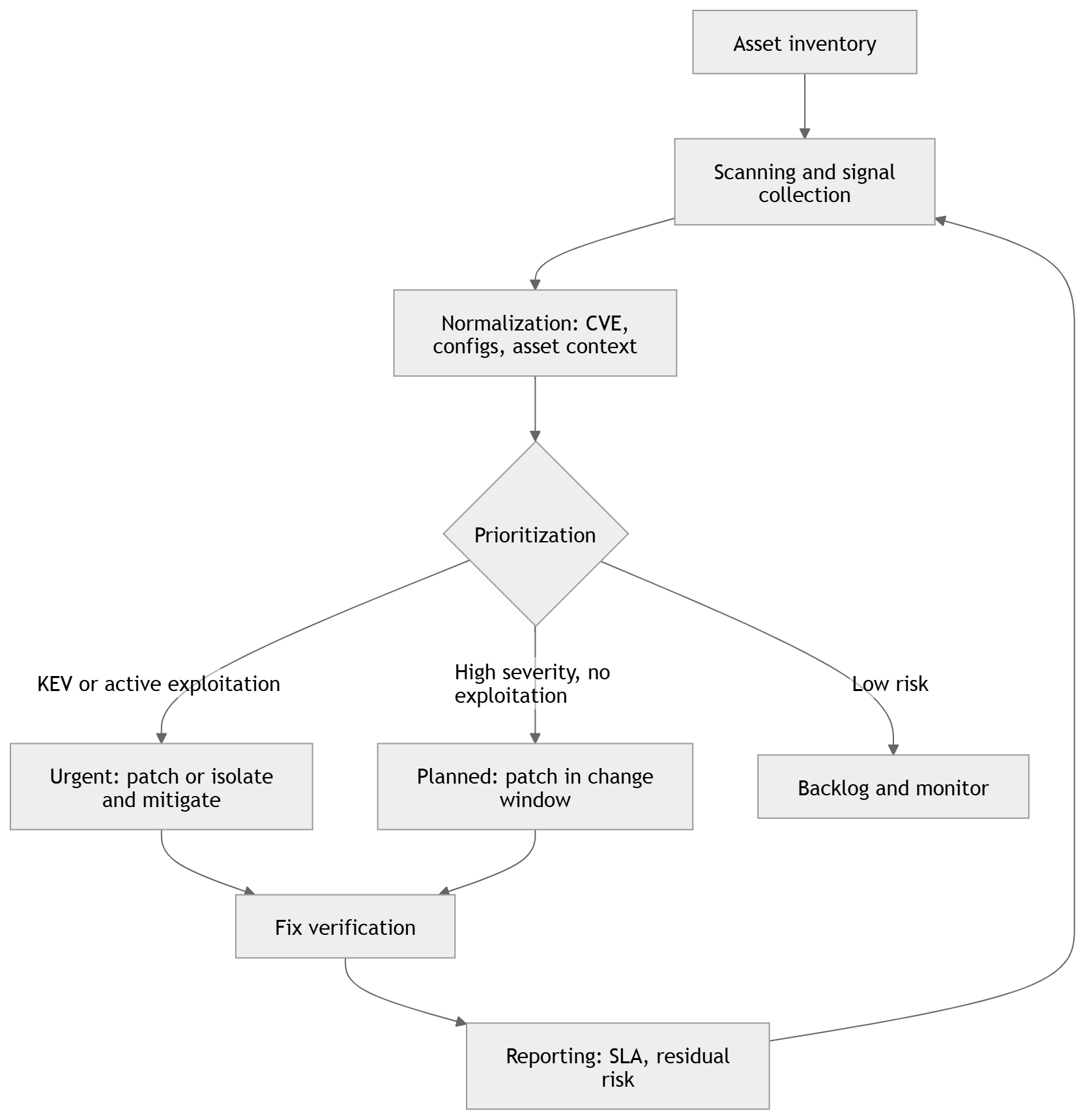
Operationalizing Vulnerability Management with TopScan
For most organizations, simply knowing that vulnerabilities exist is not enough — they also need a way to continuously find, prioritise, and fix them. This is where vulnerability management platforms such as TopScan come in.
TopScan helps you manage vulnerabilities across your internet-facing assets. You can add targets, run scheduled or ad-hoc scans, and track changes over time. TopScan aggregates results from proven scanning engines, reduces duplicates, and highlights a fix-first list based on exposure and simple business context.
It aggregates results from multiple scanning engines, enriches them with context, and helps security teams focus on higher-risk issues first by highlighting the most urgent findings. Because TopScan integrates with existing tools such as ticketing systems and CI/CD pipelines, vulnerability data flows directly into the workflows your teams already use, turning vulnerability management from a one-off security check into an ongoing, repeatable process.
Below is a simple vulnerability management cycle you can repeat weekly or daily, depending on system criticality.
How Are Vulnerabilities Identified in Cybersecurity?
Knowing how to discover and fix vulnerabilities is a core skill for a cybersecurity team. The following steps of the process are explained in detail.
Security experts use a mix of manual testing and automated tools to find system vulnerabilities. A common starting point is vulnerability scanning.
Vulnerability Scanners
These tools scan systems automatically and detect known vulnerabilities and configuration errors. They operate by matching system data to known problem databases like the CVE (Common Vulnerabilities and Exposures) list.
Common vulnerability scanners include:
- Nessus: A widely used scanner that detects a broad range of known vulnerabilities and misconfigurations.
- Qualys: A cloud-based service used for continuous scanning and compliance checks.
- OpenVAS: An open-source scanner that detects a wide range of known vulnerabilities.
|
Tool |
Deployment model |
Best at scanning |
What to watch for |
|
Tenable Nessus |
Self-hosted scanner you deploy on your own platform (Tenable positions it as deployable across many platforms). Agentless remote scanning, with optional secured credentials for deeper checks. |
Network and host vulnerability assessment with deeper local exposure detection via authenticated (credentialed) checks. Broad coverage via a large plugin library with frequent updates. |
Unauthenticated scans can rely on banner info that may be inconclusive or wrong, so plan for credentialed scans and credential management. Also, results and coverage track plugin/feed updates - keep them current. |
|
Qualys VMDR |
Cloud platform (Qualys Enterprise TruRisk Platform) with sensors: scanner appliances for network-based scanning (virtual or physical) and Cloud Agents for continuous visibility. |
Vulnerability and configuration assessment across a broad attack surface, plus asset discovery and prioritization features inside VMDR. Patch detection and CVE correlation are explicitly part of VMDR positioning. |
Internal network IP scanning requires deploying scanner appliances where they have reachability - plan placement, routing, and permissions early. Decide upfront where you want agent-based coverage vs appliance-based scanning, because it affects rollout and visibility. |
|
OpenVAS / Greenbone |
Self-hosted, feed-driven scanner: you can run the Greenbone Community Edition via Docker containers, and Greenbone also offers an "OpenVAS Free" entry-level virtual appliance that uses the Community Feed. Coverage varies by feed (Community vs Enterprise). |
Authenticated and unauthenticated testing across many protocols, with vulnerability tests delivered via a feed that is updated daily. Good fit when you want a self-hosted network vulnerability scanner and can maintain the stack. |
Community Feed is "basic coverage" and may not include checks for some enterprise products and certain compliance content, so expectations and scope matter. "OpenVAS Free" is positioned as entry-level with limited functions, so it may be restrictive for production use. |
These tools help identify outdated software, weak credentials, exposed ports, and missing patches.
Common Vulnerabilities and Exposures Examples
The CVE database lists real-world examples of vulnerabilities that have been reported globally. These entries usually include:
- A unique ID (for example, CVE-2024-5678)
- A short description of the flaw
- The affected systems or software
- Severity information and references to fixes or mitigations
By matching scan results with this database, organisations can see exactly where they’re exposed and how serious the risk is.
Final Words
The vulnerabilities in cybersecurity are like cracks in the digital wall that are hard to see but potentially devastating when not addressed. These cracks can be in the software, be caused by lax network configurations or merely caused by human error, and they provide the access needed by the attackers. That is why it is important to understand what a vulnerability is and how it can be exploited.
Most of the threats and vulnerabilities to information security can be avoided with the proper tools, frequent scans, and basic security habits, such as strong passwords and software updates. Early awareness and timely fixes can protect your data and systems. In the end, a little awareness goes a long way in keeping systems safe.

