Software flaws continue to accumulate rapidly. Fortress Information Security reported a large NVD analysis backlog in 2025, highlighting how difficult it is for defenders to keep up with newly disclosed vulnerabilities.
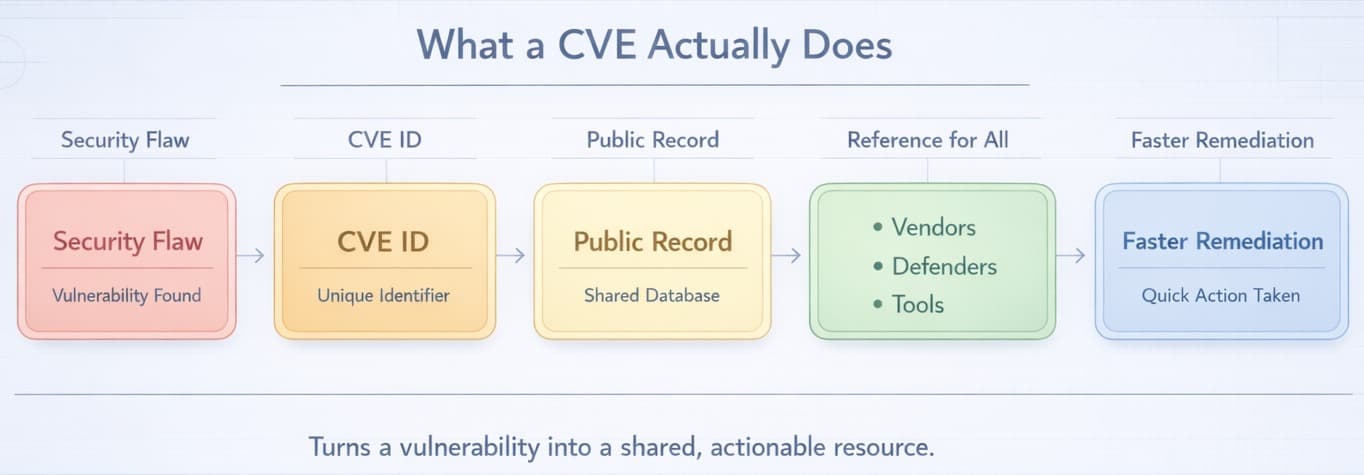
This growing backlog shows how hard it is to stay ahead of emerging threats. The CVE system helps by giving publicly known vulnerabilities a common identifier. A CVE gives each known security flaw a unique ID and public record. This makes it easier for IT teams, developers, and security pros to track problems and fix them before they are exploited.
Let’s learn what a CVE is and how to manage vulnerabilities more effectively.
What Does CVE Stand For
CVE stands for Common Vulnerabilities and Exposures. It is a standardized naming system used to identify and catalog known security flaws in software and hardware.
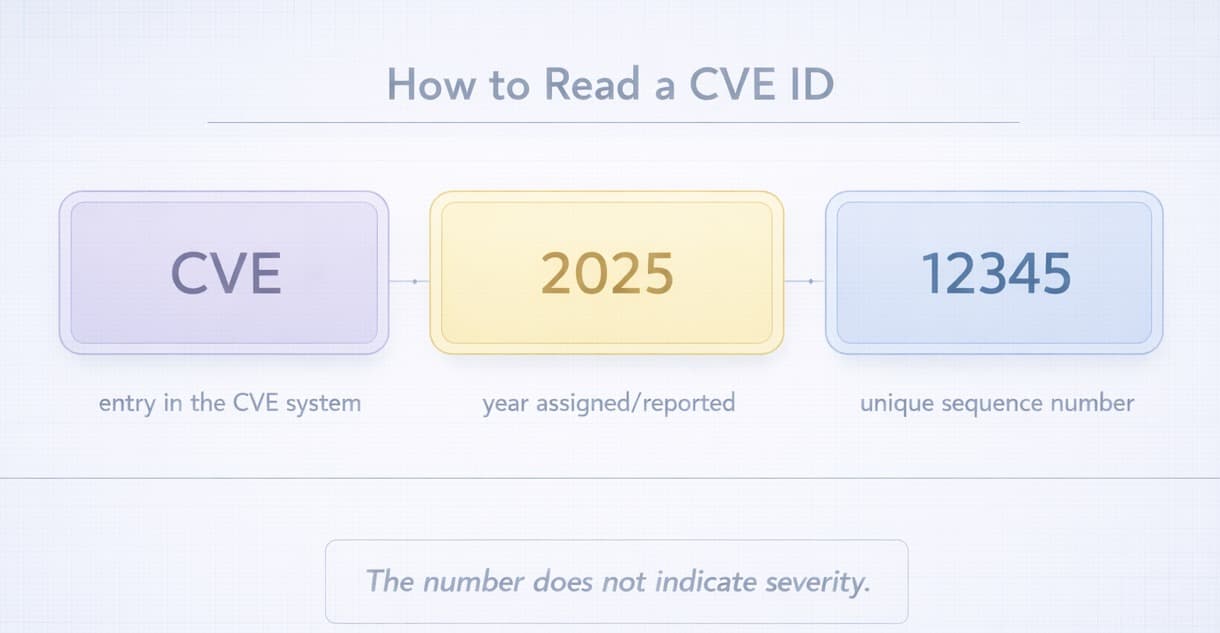
Each CVE gets a unique ID. The ID uses the format CVE-[YEAR]-[NUMBER]. For example, CVE-2021-44228 refers to a flaw published in 2021. The number does not reflect severity. It is simply a unique identifier. This avoids confusion when referring to particular vulnerability. The CVE Program is operated by MITRE and sponsored by the U.S. government through DHS and CISA. CVE IDs are assigned by MITRE and by authorized CVE Numbering Authorities, or CNAs.
The purpose of the CVE system is to give security teams, developers, vendors, and IT staff a shared way to identify and discuss known vulnerabilities.
Purpose of the CVE System
The CVE system provides an open and standardized way to track and share information about known security flaws. Without the standard system, the security teams, software sellers, and users would have to talk about different problems and understand the level of the threat.
The system helps by assigning a unique CVE ID to each vulnerability:
- Avoid confusion when discussing security issues.
- Track the vulnerabilities that are known in diverse tools and systems.
- Prioritize and remediate vulnerabilities using consistent references.
By using the same references, the CVE system also helps security tools like patch managers and scanners function more efficiently. Additionally, it speeds up communication and helps organizations respond to known flaws before attackers exploit them.
How Are CVEs Created and Numbered
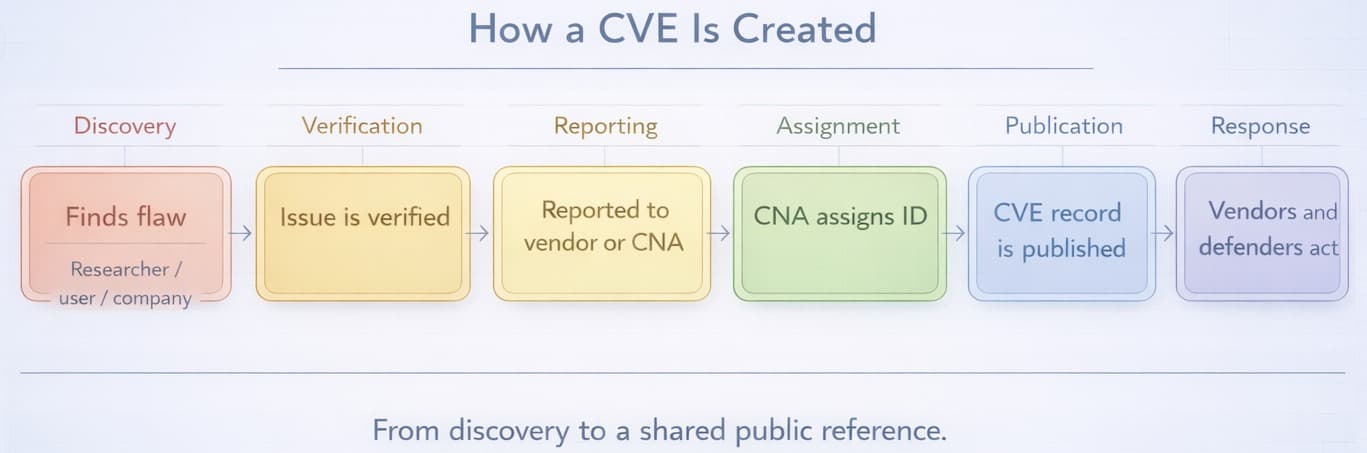
Every CVE starts with someone spotting a security flaw. This could be a regular user, a business, or a security researcher. After the problem has been verified, it is reported to software companies like Microsoft or Google or a reliable group known as a CVE Numbering Authority (CNA), such as MITRE.
After review, the CNA assigns the vulnerability a unique ID. The format of this ID is standard, such as CVE-2025-12345.
Once the CVE is assigned, the record is published so that security teams and vendors can reference it publicly. This helps security teams and the general community to be aware of the problem and take measures to address the issue.
What Is a CVSS Score
A CVSS score is a figure used to estimate the severity of a security vulnerability. It assists individuals in realizing the level of risk that a flaw may cause when it has not been corrected. That value is determined by what is known as the Common Vulnerability Scoring System (CVSS) and tends to have a range of scores between 0 and 10.
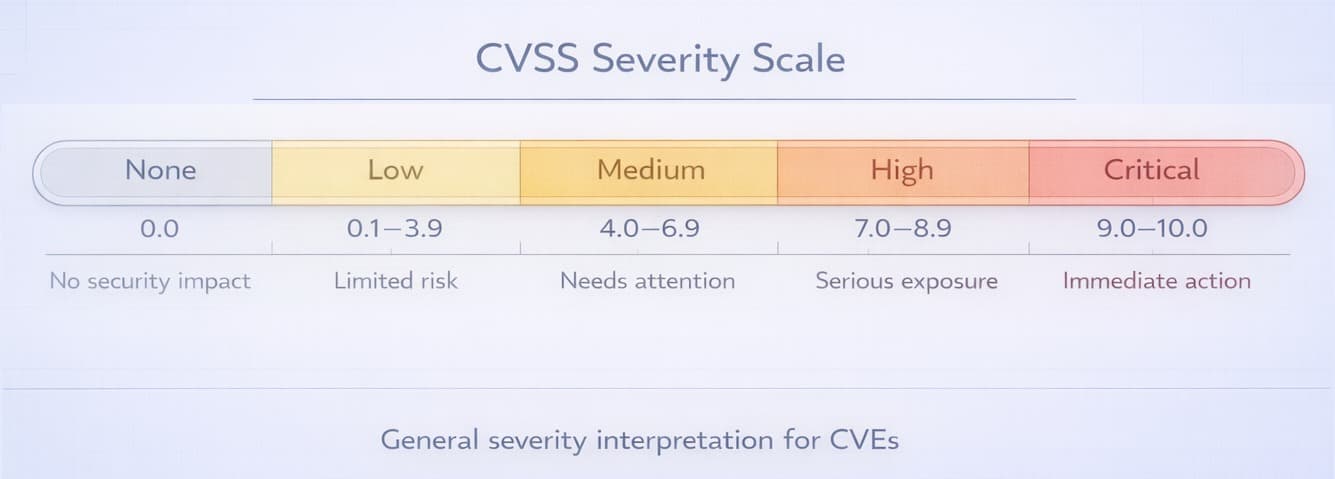
The score is based on the ease of exploitation of the vulnerability, its usability by a remote user, as well as the potential effects of the vulnerability on the system.
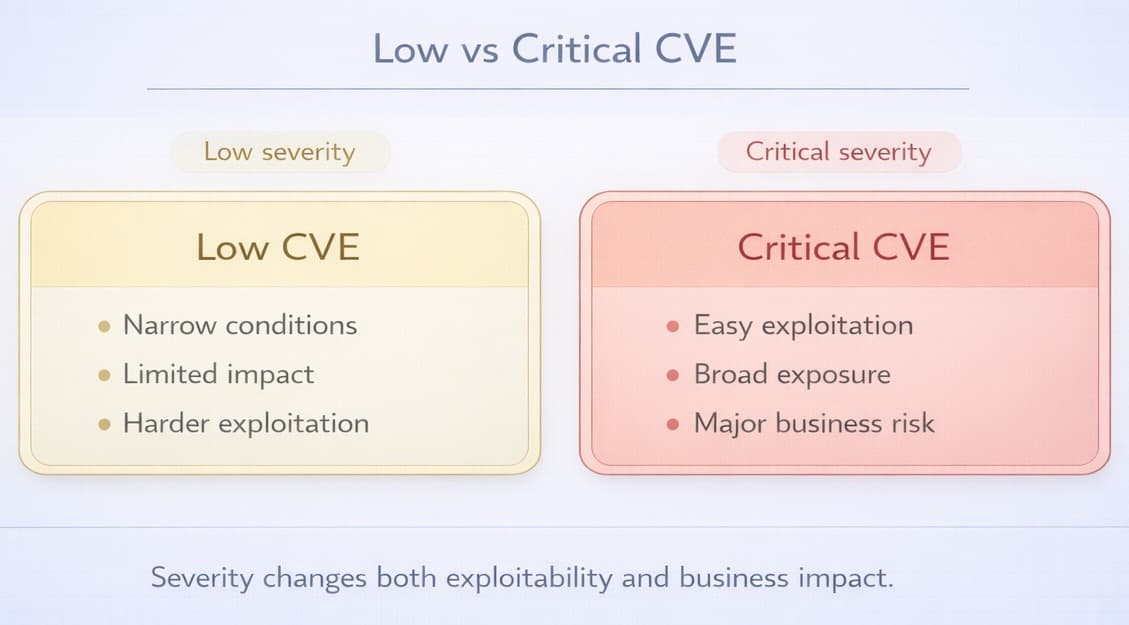
A critical vulnerability may allow an attacker to gain remote control of an internet-facing system, whereas a low-risk CVE may enable only minor changes when very particular circumstances are met.
The CVE score will assist an organization in knowing when the issues need to be fixed urgently and by priority.
Some Examples of Notable CVEs
Some CVE vulnerabilities have contributed significantly to cybersecurity globally over the past years. These famous examples show that even a slight misconduct can be disastrous.
Here are a few notable examples:
- CVE-2017-0144 EternalBlue: This was a vulnerability known to be in Microsoft Windows. It was deployed in the WannaCry ransomware attack. The vulnerability resulted in worldwide disruption and huge disruption in 2017.
- CVE-2021-44228 Log4Shell: A severe vulnerability of the widely-used Log4j API of the logging software in Java applications. It enabled hackers to have access to systems remotely and was regarded as one of the most terrifying vulnerabilities in recent years.
- CVE-2014-0160 Heartbleed: Present as a vulnerability in the OpenSSL library of desktop and laptop encryption, this bug may allow hackers to steal valuable data such as passwords and encryption keys.
This is one of the reasons why CVE tracking and patching should be done. An unpatched vulnerability can lead to significant consequences for people and governments.
How Can You Track and Manage CVEs
Monitoring and managing security flaws are among the primary concerns of system security. Fortunately, some tools and resources can keep IT teams and security professionals up to date.
Some common ways to track and manage CVEs include:
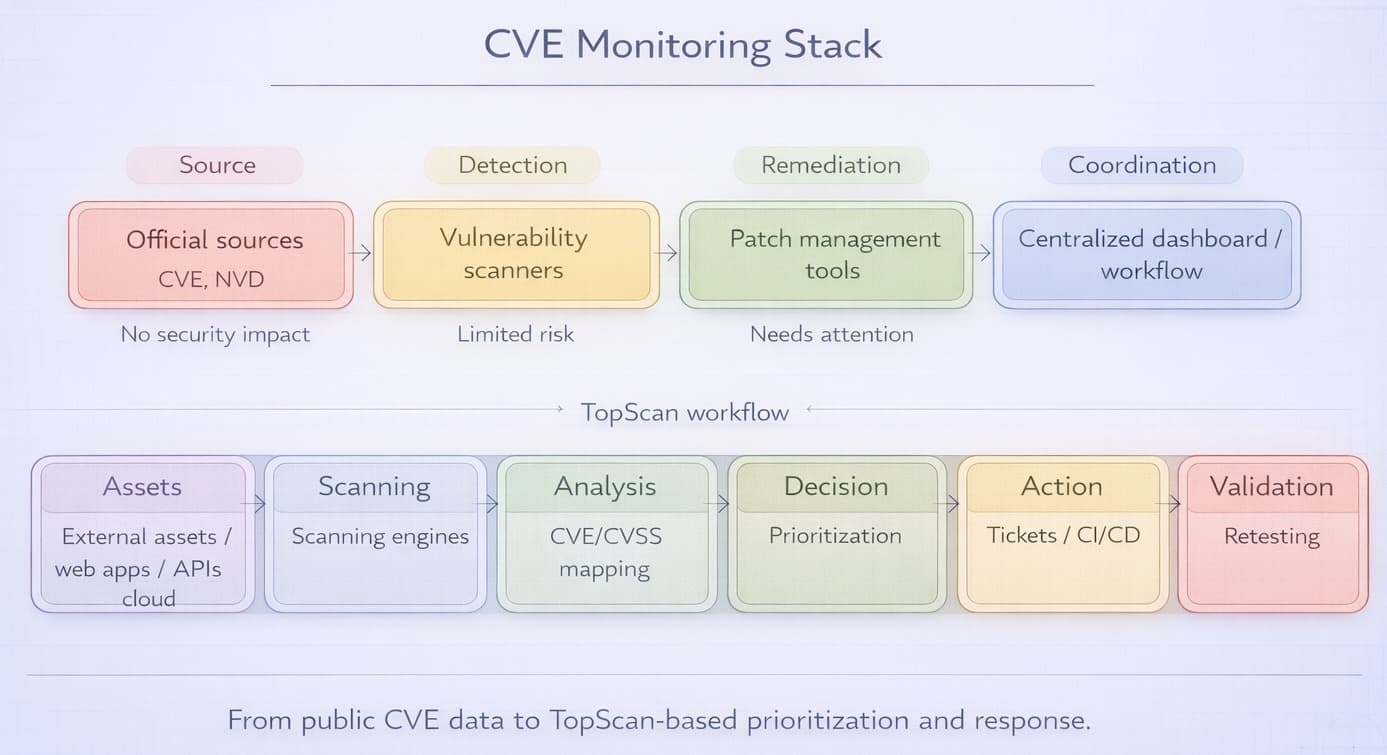
- Official sources: The CVE list maintained through the CVE Program and the National Vulnerability Database (NVD) provide public information about known CVEs.
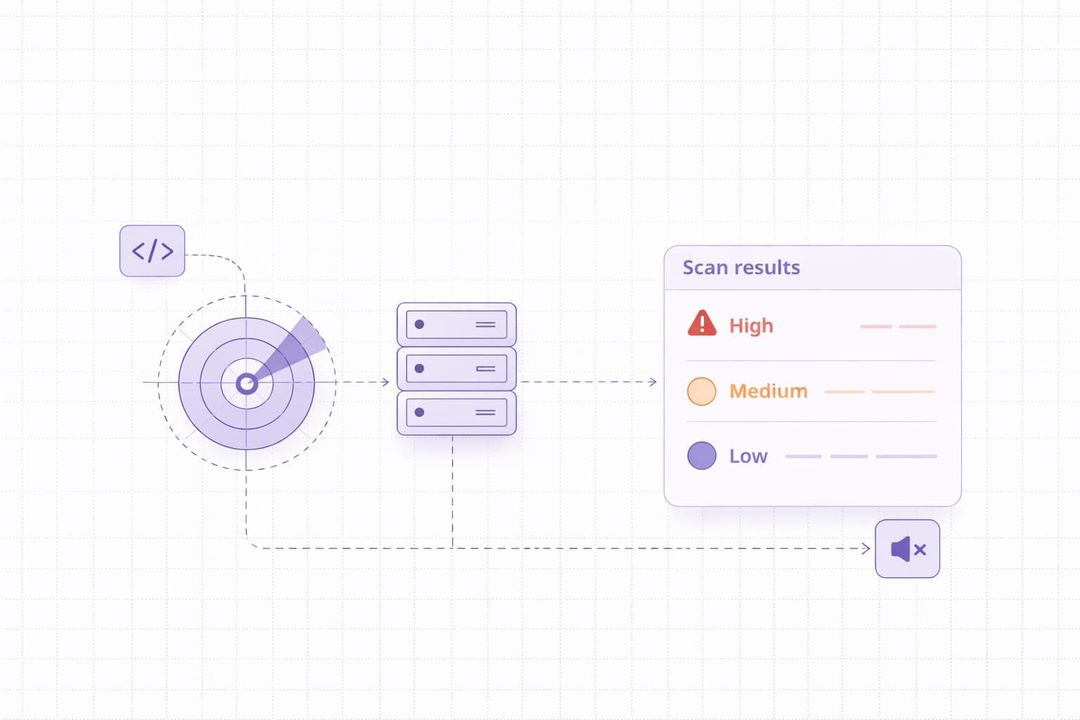
- Security tools: Vulnerability scanners and related security tools can scan systems automatically to look for known CVEs.
- Patch management software: These are programs used to determine the patches to be installed to correct vulnerabilities.
Some tools are hard to set up, and they need a full security team. That is why platforms like TopScan are gaining popularity.
TopScan is built for small and mid-sized companies that want simpler CVE and vulnerability management workflows. It uses trusted open-source tools like Nmap and OpenVAS, and adds smart features like:
- Automated vulnerability ranking.
- Automated retesting after fixes.
- Clear, easy-to-read reports.
TopScan works across cloud environments, internal networks, web applications, and APIs. It also supports compliance with standards like PCI DSS, ISO 27001, and SOC 2. If your team wants to catch issues before attackers do, TopScan is a great place to start.
Simplifying CVE Management with TopScan
Managing CVEs manually or with multiple disconnected tools can quickly become overwhelming, especially for small and mid-sized teams. Platforms like TopScan help centralise this work. TopScan continuously scans your external perimeter, web applications, APIs, and cloud assets using engines such as Nmap, OpenVAS, and Nuclei, then maps findings to CVE and CVSS data in a single dashboard.
Built-in prioritisation highlights the vulnerabilities that are most likely to be exploited, and integrations with ticketing systems and CI/CD pipelines ensure that fixes are assigned and tracked instead of getting lost in spreadsheets. For organisations that do not have a large security department, this kind of automation turns CVE tracking from a manual chore into an ongoing, manageable process.
Types of Vulnerabilities Listed in CVEs
There are various security vulnerability types that CVEs may address, depending on the influence that a vulnerability has on software or hardware. Knowledge of the common categories enables teams to identify and rectify issues more quickly.
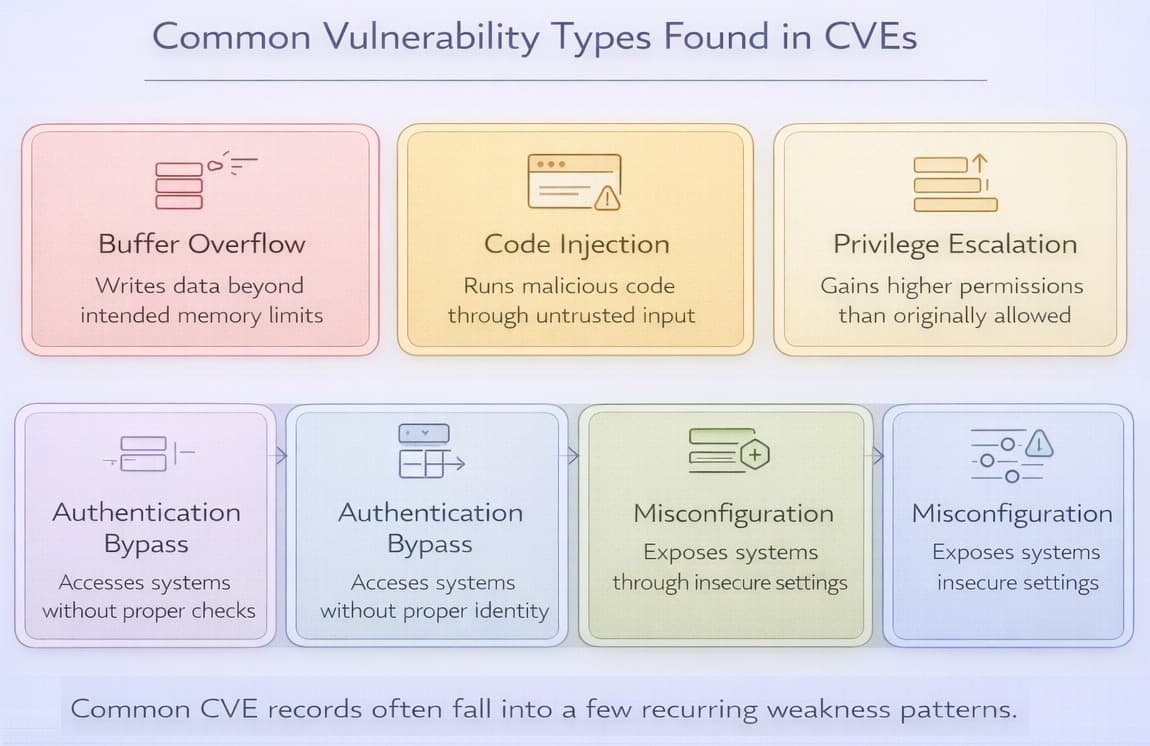
The following are some of the principal types:
- Buffer overflows: Sending more data than a program expects can cause crashes or allow an attacker to execute malicious code.
- Code injection: An attacker tries to inject some malicious code into a program, most often through user supplied data, so as to be able to control or access information.
- Privilege escalation: This is a flaw that allows a user or attacker to gain more access than normally permitted.
- Authentication bypass: Weaknesses that allow attackers to bypass login checks or gain unauthorized access without valid credentials.
- Misconfigurations: These include wrong settings that allow attacks on systems with ease.
Every CVE explains the nature of the vulnerability to enable the developers, security teams, and users to know what is amiss and how they can resolve the problem.
How Do Hackers Exploit CVEs
Attackers can scan for vulnerable systems using automated tools by using known vulnerabilities that have not yet been patched. Such weaknesses are frequently simple to identify with the help of open CVE repositories, particularly in the event that fixes have failed to be installed.
This is how exploitation normally occurs:
- Hackers can search vulnerable systems using an automated tool.
- They launch code or a script designed to exploit the weakness.
- After gaining access, they can steal data, deploy malware, or move deeper into a network.
A small part of CVEs are in use by real-world attackers and might even be exploited in the wild before many folks are even aware of the vulnerability. This is why patching systems should be done promptly and CVE reports should be observed on a regular basis.
What Should You Do When a New CVE Is Released
It is essential to respond quickly when a new CVE affecting your systems is published. Even though there could be a potential possibility that the vulnerability has not been used yet, the greater the delay, the greater the risk of being attacked.
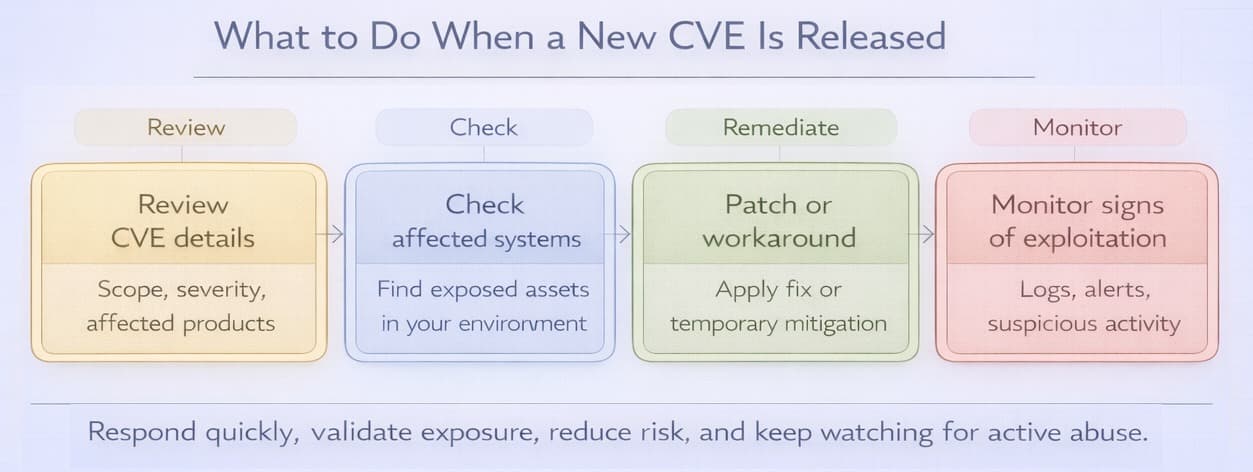
This is what you should do:
- Review the CVE details. Scan the description, look at the main CVSS value, and be aware of which software or systems have been compromised.
- Check whether your systems are affected. Find out what systems you may have been using that are infected.
- Install patches/updates. An update should be installed immediately. If you fail to do so, find a workaround.
- Monitor any signs of exploitation. Look for strange behaviour on your system or alerts that could point to a possible attack.
A good vulnerability management process will help you react to the latest CVEs promptly and protect your data and systems.
How Often Are New CVEs Released
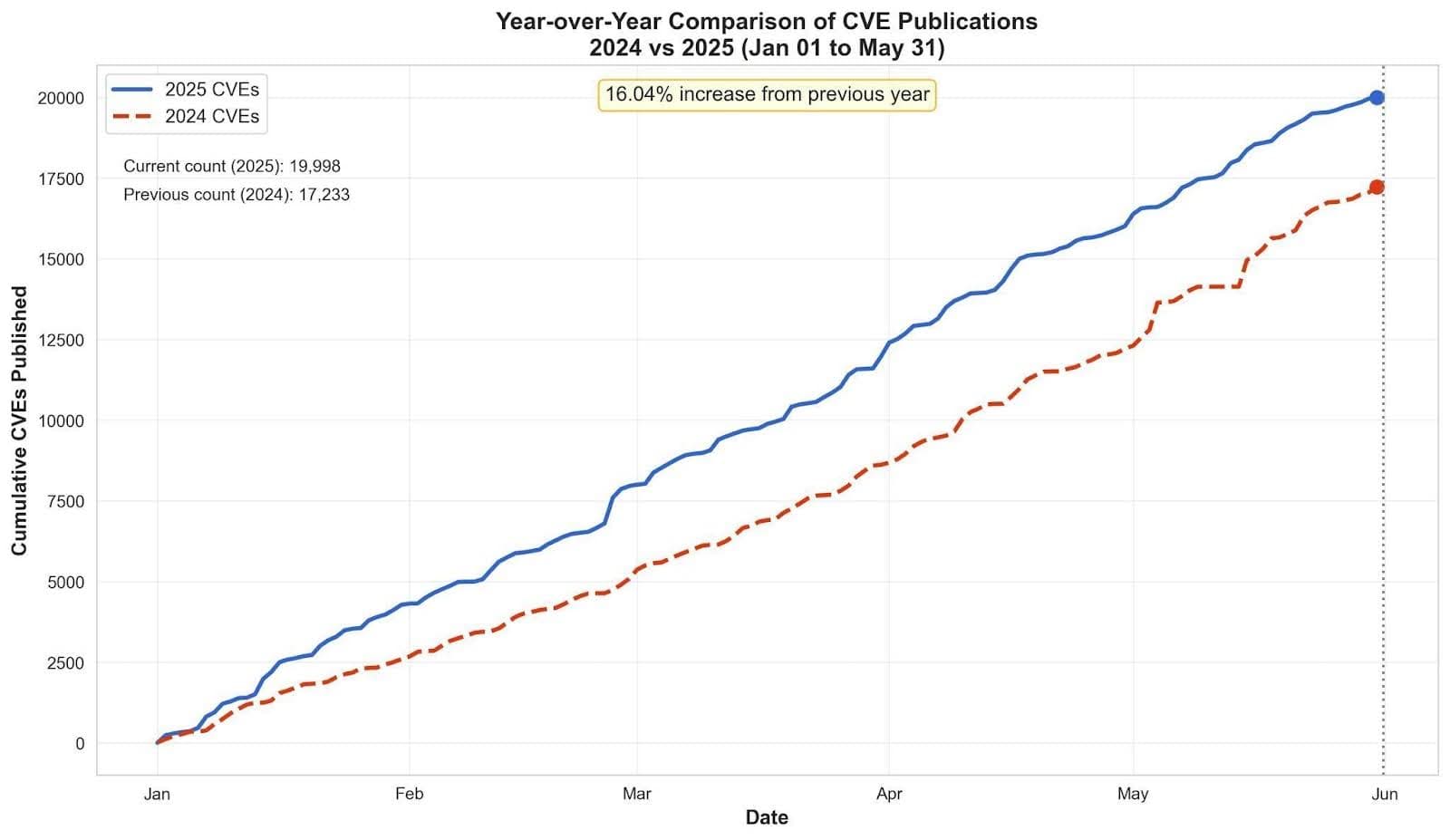
New CVEs are published almost every day. Due to the ever-increasing nature of software and technology, security teams and researchers keep finding vulnerabilities. Thousands of CVEs are added to public databases every year.
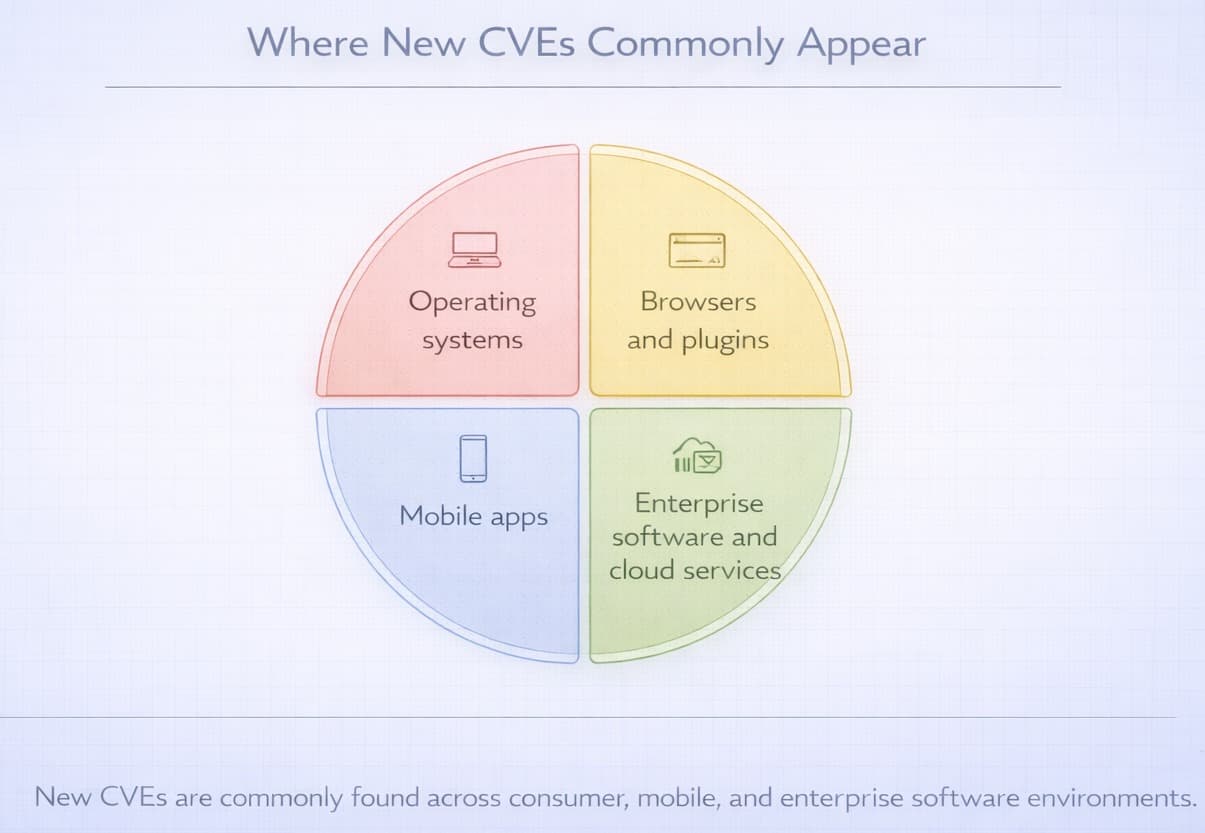
As the CVEs are still increasing, organizations are advised to keep abreast of the changes. These sources are relatively easy to monitor using automated tools that alert teams to newly disclosed issues.
Monitoring the new CVEs enables businesses and individuals to address the problems within a short period and avoid the chances of breach.
CVE Governance & Programs
CVE Program is operated by MITRE Corporation, and sponsored by CISA Cybersecurity and Infrastructure Security Agency. CVE.org is the official public website of the CVE Program maintained by MITRE.
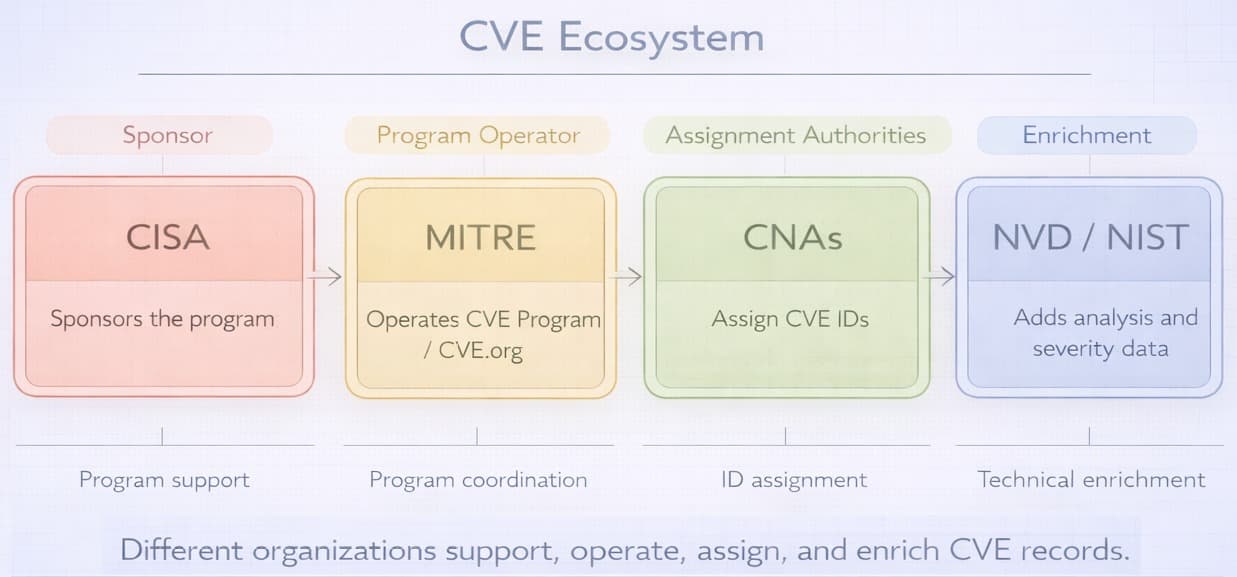
MITRE also plays a central role in the CNA ecosystem that assigns CVE IDs. Such organizations have the permission to attach CVE IDs to vulnerabilities that they find or are reported to them.
The National Institute of Standards and Technology NIST supports the ecosystem through the National Vulnerability Database (NVD), which enriches CVE records with severity scoring and technical analysis.
Final Thoughts
Common Vulnerabilities and Exposures are an essential part of how the security community tracks and communicates known flaws. They provide a standardized way to report, track, and discuss security issues across products and systems.
Security experts, organizations, and developers, through the use of the system, can quickly identify vulnerabilities and their severity. It enables them to respond more consistently and reduce the risk of unpatched known vulnerabilities.