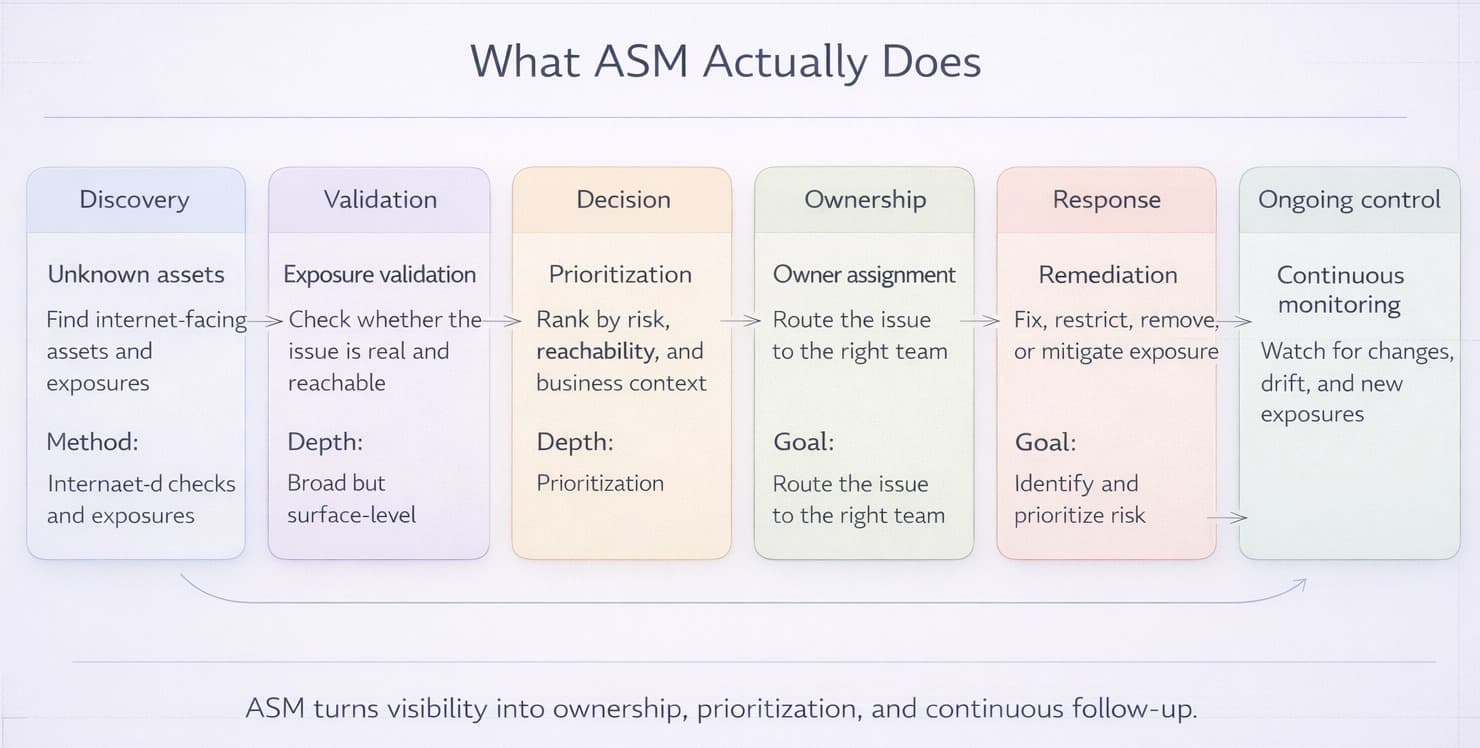
Attack Surface Management (ASM) continuously discovers, classifies, and prioritizes potential entry points and exposures across an organization’s digital infrastructure. By contrast, comprehensive cybersecurity programs safeguard an organization’s networks, applications, cloud services, and other digital assets through policies, processes, and technical controls. At a practical level, ASM helps teams discover unknown internet-facing assets, exposed services, expired certificates, weak configurations, and orphaned integrations before attackers abuse them.
Systematic security management mitigates exposure to cyber-attacks by achieving full attack-surface visibility and correcting vulnerabilities before criminals can exploit them. This helps organizations improve visibility and respond to exposures earlier. Threat actors continue to refine their reconnaissance techniques, and new attack vectors emerge constantly.
Instead of starting with market size, start with operational reality: defenders need to know what is exposed, what is internet-facing, and what is already being actively exploited. Signals such as CISA's Known Exploited Vulnerabilities catalog and repeated warnings about exposed edge devices are more useful to practitioners than market forecasts. This explosive growth reflects the critical importance organizations place on understanding and managing their digital attack surfaces.
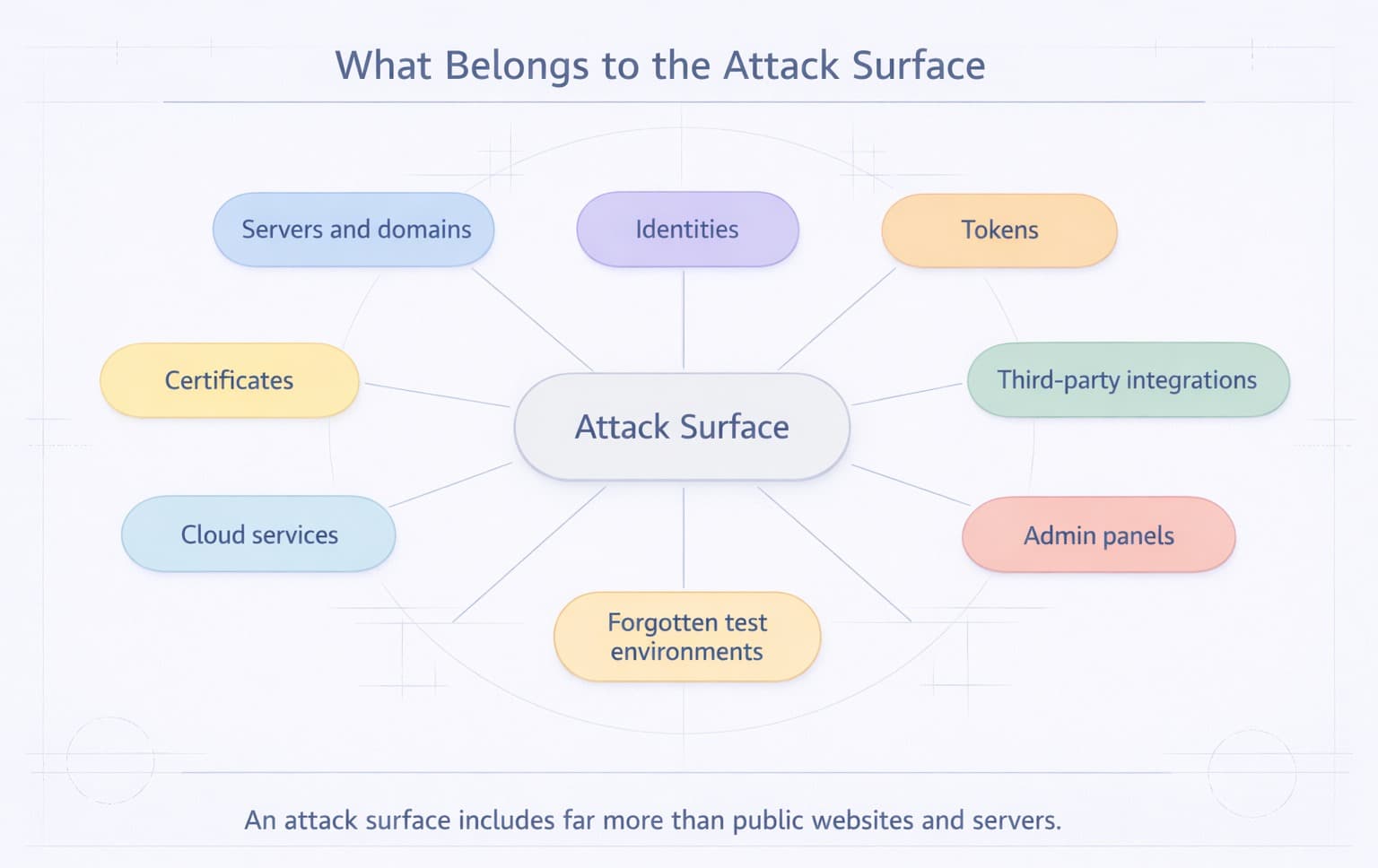
According to NIST SP 800-172, an attack surface represents "the set of points on the boundary of a system, a system element, or an environment where an attacker can try to enter, cause an effect on, or extract data from that system, system element, or environment." In simple terms, your attack surface is everything an attacker can discover, reach, misuse, or pivot through. That includes not only servers and domains, but also identities, tokens, third-party integrations, admin panels, forgotten test environments, and externally reachable cloud services.
ASM improves visibility, but its value comes from turning visibility into action: identifying what is reachable, understanding who owns it, checking whether it is exposed to active exploitation, and pushing the right issue to the right team fast. Implementing ASM therefore strengthens the organization’s overall security posture and increases confidence among stakeholders and customers.
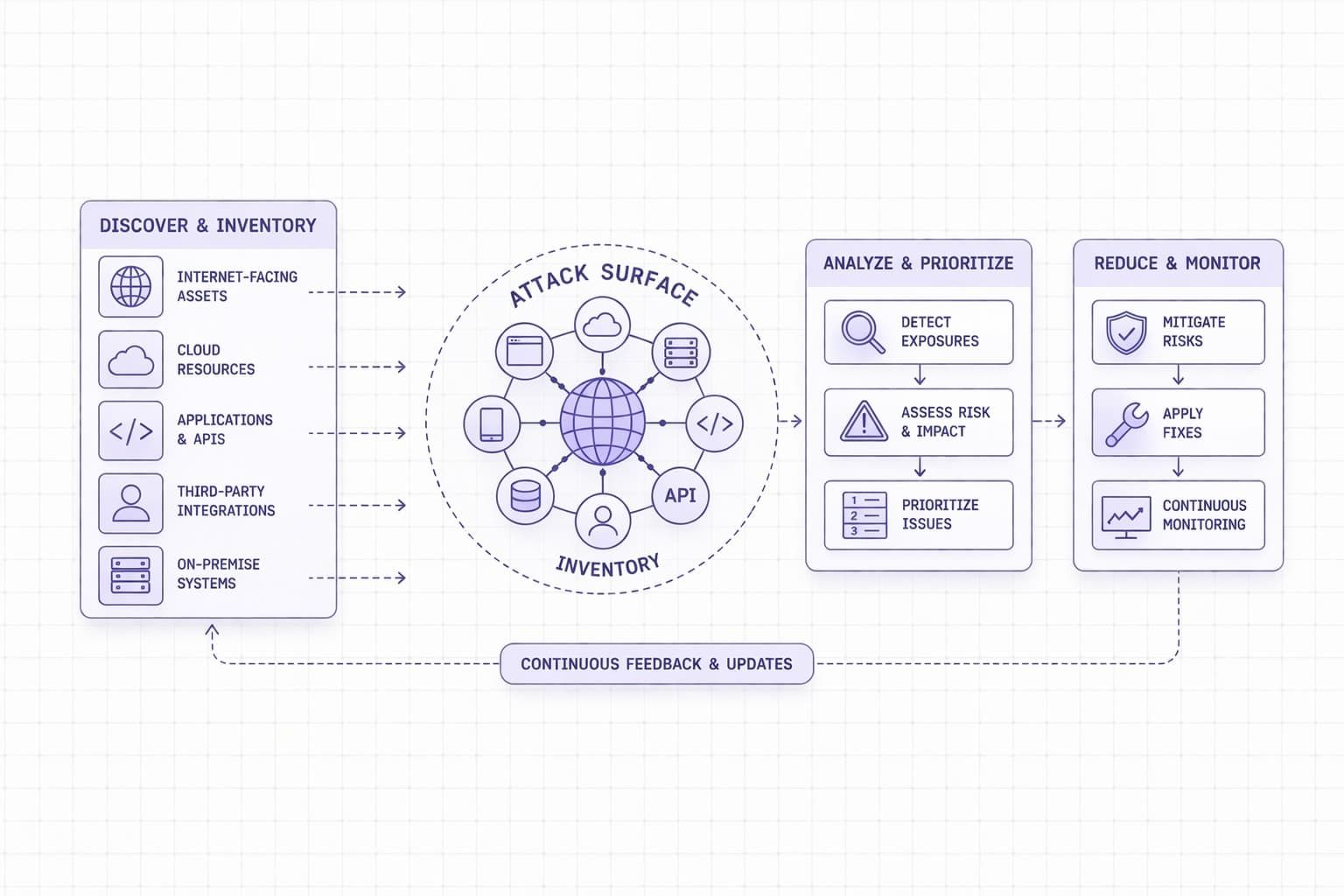
Key Components of the ASM Lifecycle
The attack surface management lifecycle recognizes that the various phases of security exposure management are interconnected and continuous. "Understanding all components helps you achieve a successful ASM program," according to IBM's cybersecurity research.
Table 1. Attack surface management lifecycle
|
Phase |
Main focus |
What to watch for |
|
Discovery & Asset Inventory |
Identify internet-facing assets such as domains, subdomains, IPs, certificates, cloud resources, SaaS apps, and APIs. |
Forgotten subdomains, abandoned projects, shadow IT, unmanaged SaaS instances, and third-party assets linked to the company. |
|
Assessment & Risk Analysis |
Check discovered assets for vulnerabilities, weak configurations, exposed services, outdated software, and authentication issues. |
Unscanned APIs, exposed admin panels, weak TLS settings, open ports, risky storage exposure, and false confidence from a single scanner. |
|
Threat Intelligence Integration |
Compare findings against active exploitation data, attacker techniques, and public advisories. |
Issues that are not just severe on paper, but are already being exploited or actively targeted. |
|
Risk Prioritization |
Rank issues by business impact, exploitability, asset criticality, and exposure level. |
High-value assets, identity-related exposure, missing ownership, and findings that create a realistic attack path. |
|
Remediation & Mitigation |
Fix or reduce exposure through patching, hardening, access restriction, secret rotation, and asset cleanup. |
Issues left open without an owner, incomplete fixes, temporary mitigations that become permanent, and repeat exposure after deployment. |
|
Continuous Monitoring |
Track changes over time and detect new assets, configuration drift, certificate changes, and fresh exposure. |
New externally reachable services, unnoticed cloud changes, and exposure introduced by releases or vendor activity. |
|
Reporting & Compliance |
Summarize exposure trends, remediation progress, ownership gaps, and risk reduction for different stakeholders. |
Dashboards without context, unresolved critical issues, repeat findings, and a growing number of assets without a clear owner. |
A practical example is the 2023 MOVEit case: CISA and the FBI reported that internet-facing MOVEit Transfer web applications were compromised with the LEMURLOOT web shell and then used for data theft. This is why public-facing services cannot be inventoried once and forgotten - they need continuous monitoring and prioritization.
Specialized Management Approaches for Different Types of Attack Surfaces
There are multiple types of attack surfaces, each type requiring its own discovery and management process.
Table 2A. Digital attack surfaces managed directly in ASM
|
Attack surface type |
What it includes |
What teams should focus on |
|
External / Internet-Facing |
Public domains, subdomains, websites, APIs, portals, VPN gateways, public IPs, certificates, and exposed services. |
Continuously discover exposed assets, validate real exposure, and prioritize issues that attackers can reach first. |
|
Internal |
Internal apps, databases, file shares, management interfaces, segmentation zones, and workstation or server networks. |
Reduce lateral movement opportunities, review segmentation, and control access to sensitive internal systems. |
|
Cloud Infrastructure |
IaaS workloads, storage, IAM roles, security groups, managed databases, serverless services, and Kubernetes environments. |
Monitor public exposure, misconfigurations, identity risks, and drift across fast-changing cloud resources. |
|
SaaS Exposure |
Collaboration suites, CRM systems, ticketing platforms, code repositories, file-sharing services, and connected SaaS apps. |
Review sharing settings, stale accounts, risky integrations, delegated access, and tenant-level governance. |
|
Identities, Secrets, and Access Paths |
User accounts, service accounts, API keys, tokens, certificates, SSH keys, and secrets used in CI/CD or cloud workflows. |
Reduce excessive privileges, rotate secrets, review service accounts, and monitor exposed credentials or risky access paths. |
|
Third-Party and Subsidiary Exposure |
Vendor-managed portals, acquired domains, partner integrations, inherited DNS, and external services linked to the organization. |
Clarify ownership, validate exposure regularly, and manage external dependencies that expand the attack surface. |
Table 2B. Adjacent attack surface domains that ASM should inform, but does not fully own
|
Domain |
What it includes |
What teams should focus on |
|
Physical |
Offices, data centers, network closets, employee devices, removable media, and badge-controlled areas. |
Protect facilities and hardware, control physical access, track assets, and reduce the risk of device theft or tampering. |
|
Human / Social Engineering |
Employees, contractors, help desk workflows, approval processes, executive communications, and vendor interactions. |
Strengthen identity checks, improve phishing resistance, review support workflows, and reduce the risk of impersonation or credential theft. |
|
Supply Chain / Business Process |
Third-party workflows, software dependencies, outsourced operations, procurement processes, and shared service relationships. |
Review vendor trust, control external access, assess dependency risk, and tighten offboarding and integration governance. |
- External Attack Surface Management (EASM) focuses specifically on internet-facing assets and services that external attackers can discover and potentially exploit. EASM provides the same reconnaissance view that threat actors obtain when targeting an organization, making it essential for understanding genuine external risk exposure.
- Internal Attack Surface Management tackles systems and services within an organization’s network. Internal assets may not be internet-facing, but if attackers breach perimeter defenses, they may use them for lateral movement and privilege escalation.
- Cloud Attack Surface Management - cloud environments present unique challenges due to their dynamic nature, shared responsibility models, and configuration complexity. Research by Google Cloud's Mandiant team shows that cloud attack surfaces require specialized tools capable of discovering ephemeral resources, analyzing cloud-specific configurations, and integrating with multiple cloud provider APIs.
Attack Surface Management Compared to Traditional Vulnerability Management
Attack surface management and vulnerability management serve complementary but distinct functions in organizational security programs.
Table 3. Attack surface management vs vulnerability management
|
Aspect |
Attack Surface Management |
Vulnerability Management |
|
Primary Focus |
External exposure discovery and mapping |
Known asset vulnerability identification |
|
Asset Scope |
Unknown, shadow IT, and external assets |
Managed, inventoried organizational systems |
|
Discovery Method |
Reconnaissance from attacker perspective |
Internal scanning of known infrastructure |
|
Risk Context |
Business exposure and attack likelihood |
Technical vulnerability severity (CVSS) |
|
Frequency |
Continuous real-time monitoring |
Scheduled periodic assessments |
|
Remediation Focus |
Attack surface reduction and exposure elimination |
Patch deployment and vulnerability fixes |
Example 1: an unknown internet-facing subdomain with an outdated admin panel is first an ASM problem, because the asset itself must be discovered.
Example 2: a known VPN gateway missing a patch is first a vulnerability management problem, because the asset is already known and the issue is patchable.
Example 3: a publicly reachable cloud storage bucket with excessive access is neither a classic CVE problem nor just an inventory problem - it is an exposure management problem that requires context and prioritization.
Essential Tools and Platforms for Effective ASM
Selecting the right tools is important, but attack surface management is not just about buying a platform with the longest feature list. In practice, effective ASM depends on how well a solution helps teams discover unknown assets, validate real exposures, assign ownership, prioritize the issues that matter most, and confirm that remediation actually happened.
Most organizations do not need a single "magic" product. They need a working combination of capabilities: external discovery, vulnerability assessment, cloud visibility, threat intelligence correlation, workflow integration, and continuous monitoring. The exact mix depends on the size of the organization, the complexity of its infrastructure, and the maturity of its security operations.
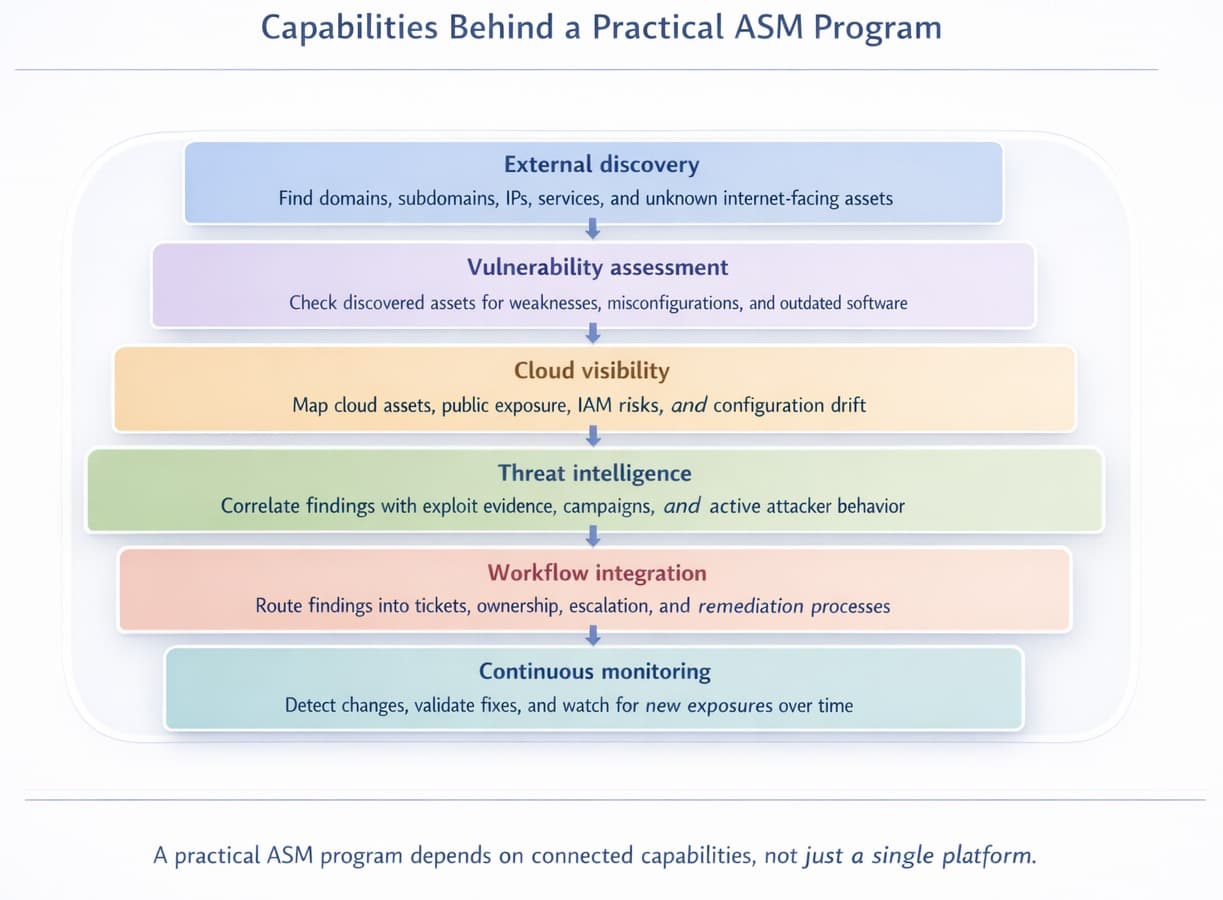
External Attack Surface Management Platforms
Dedicated EASM platforms help organizations discover and monitor internet-facing assets such as domains, subdomains, public IPs, certificates, web applications, APIs, VPN gateways, and exposed services. Their main value is not only in listing assets, but in showing what an attacker can actually find from outside the organization.
Leading solutions in this category typically provide continuous discovery, exposure validation, change detection, and risk-based prioritization. They are most useful when they can connect technical findings to business context, ownership, and real remediation workflows.
Some platforms also combine EASM with continuous vulnerability scanning and multi-engine validation. For example, solutions such as TopScan can orchestrate multiple scanning engines, consolidate overlapping results, and present them in a single dashboard that supports practical prioritization. This helps security and IT teams move from occasional external scans to an ongoing process tied to real infrastructure changes and follow-up actions.
Supporting Tool Categories
ASM platforms rarely work in isolation. In mature environments, they are usually supported by several adjacent tool categories:
- Asset discovery and enumeration tools help identify domains, certificates, IP ranges, cloud resources, and external services that may not appear in internal inventories.
- Vulnerability assessment tools help analyze the security of discovered assets by detecting outdated software, misconfigurations, weak services, and other technical exposures.
- Cloud security tools help map public exposure, risky identities, excessive permissions, and configuration drift across IaaS, PaaS, containers, and serverless environments.
- Threat intelligence platforms help distinguish between theoretical weaknesses and exposures tied to active exploitation, known attacker behavior, or sector-specific campaigns.
- Workflow and ticketing integrations help turn findings into action by assigning ownership, creating remediation tasks, and tracking closure.
Before investing in an ASM platform, organizations should evaluate not only feature lists, but also how effectively the tool supports real operational work. In practice, the best solutions do more than discover assets - they help teams validate exposures, assign ownership, prioritize what matters most, and confirm that remediation actually happened. The table below outlines the most important capabilities to assess when comparing ASM tools in a demo or pilot.
Table 4. How to evaluate ASM tools in practice
|
Capability |
Why it matters |
Question to ask in a demo |
|
Unknown asset discovery |
Many organizations do not struggle with scanning known assets - they struggle with finding assets they did not know they had. A strong ASM platform should help uncover shadow IT, forgotten subdomains, abandoned projects, and third-party internet-facing assets. |
Show how your platform discovers assets that are not already listed in our CMDB or asset inventory. |
|
External attack surface visibility |
ASM is most valuable when it shows what an attacker can actually see from outside. If the platform cannot map the public-facing footprint clearly, it will miss important exposure paths. |
Show the full external view of an organization, including domains, subdomains, certificates, public IPs, and exposed services. |
|
Asset attribution |
Discovery is much less useful if teams cannot tell why an asset belongs to them. Analysts need evidence that links the asset to the organization. |
How do you prove that a discovered asset belongs to our company, subsidiary, or vendor ecosystem? |
|
Continuous monitoring |
Attack surfaces change constantly because of deployments, DNS updates, cloud changes, and third-party activity. One-time scans are not enough. |
How quickly does the platform detect a new internet-facing asset or a meaningful change to an existing one? |
|
Exposure validation |
Teams lose trust in tools that generate noisy findings without checking whether an issue is real, reachable, and relevant. |
How do you validate that a finding is genuinely exposed and not just theoretically present? |
|
Risk-based prioritization |
Security teams need help deciding what matters now, not just what exists. Prioritization should go beyond raw severity scores. |
Can you prioritize findings using exploit evidence, internet exposure, asset criticality, and business context rather than CVSS alone? |
|
Threat intelligence correlation |
A platform becomes more practical when it can distinguish between a generic weakness and an exposure linked to active attacker behavior. |
Can you correlate findings with active exploitation evidence, known campaigns, or threat intelligence sources? |
|
Identity and access context |
Many serious exposures involve identities, tokens, service accounts, and access paths rather than just vulnerable hosts. |
Can the platform identify risky identities, exposed credentials, or internet-facing services tied to privileged access? |
|
Cloud visibility |
Modern attack surfaces extend deeply into cloud infrastructure, and many critical exposures come from misconfigurations rather than classic software flaws. |
Show how the platform maps cloud assets, public exposure, IAM risks, and misconfigurations across providers. |
|
SaaS visibility |
Sensitive data and risky access often live in SaaS platforms that traditional network tools do not cover well. |
Can you show how the platform identifies exposed SaaS tenants, risky sharing, stale accounts, or unsafe integrations? |
|
API and application coverage |
A large part of the modern external surface includes APIs, web apps, authentication endpoints, and developer-facing services. |
How do you discover and assess APIs, login portals, developer tools, and internet-facing application components? |
|
Evidence quality |
Analysts need enough detail to trust the finding and route it correctly. Weak evidence slows triage and creates friction with asset owners. |
What evidence does each finding include - for example screenshots, HTTP responses, DNS records, certificates, service banners, or configuration details? |
|
Workflow integration |
A tool only adds value if findings can move into existing remediation processes instead of living in a separate dashboard forever. |
Can you create tickets, push alerts, sync status, and integrate with our existing security and IT workflows? |
|
Ownership mapping |
Remediation slows down when no one knows who owns the exposed asset. Good ASM should help connect findings to responsible teams. |
How does the platform map discovered assets to business units, environments, and technical owners? |
|
Retesting and closure verification |
Teams need to confirm whether a fix actually worked. Otherwise, closed tickets may hide still-exposed assets. |
After remediation, can the platform automatically rescan the asset and verify whether the exposure is truly gone? |
|
Coverage transparency |
Every platform has blind spots. Buyers need to understand where visibility is strong and where it is incomplete. |
Where does your visibility depend on external signals, APIs, agents, authenticated access, or customer-supplied data? |
|
Multi-engine support |
No single engine catches everything. Combining multiple discovery and scanning methods often improves accuracy and depth. |
Which discovery and assessment engines are used under the hood, and how do you handle overlapping or conflicting results? |
|
Reporting for different audiences |
Security teams, managers, and executives need different levels of detail. Reporting should support action, accountability, and trend tracking. |
Can you show technical findings for analysts, ownership views for remediation teams, and trend summaries for leadership? |
|
Time-to-value |
Some tools look strong in demos but require long setup and heavy tuning before they become useful. |
What can a customer realistically see in the first 7, 14, and 30 days after onboarding? |
|
Practical fit for lean teams |
Many SMB and mid-market teams need automation and clarity more than enterprise-scale complexity. |
What parts of discovery, prioritization, and follow-up are automated for a small security or IT team? |
No ASM program succeeds on tooling alone. Even strong platforms become ineffective if ownership is unclear, discovery is not continuous, or findings do not flow into remediation. For that reason, organizations should treat tool selection as one part of a larger operating model that includes governance, prioritization, collaboration between teams, and regular reassessment of the external environment.
This also explains why continuous attack surface management matters more than periodic review. Modern environments change too quickly for quarterly snapshots to provide enough protection. The next step is therefore to understand how organizations turn ASM from a toolset into an ongoing process.
How do organizations implement continuous attack surface management
First 30 days of ASM:
- Days 1-7: build the initial baseline of domains, subdomains, IP ranges, cloud accounts, and externally reachable services.
- Days 8-14: classify assets by business function, environment, internet exposure, and owner.
- Days 15-21: identify critical exposures and define response paths for security, infrastructure, cloud, and application teams.
- Days 22-30: set up recurring discovery, alert thresholds, ticketing, and a small KPI set for time-to-detect, time-to-triage, and time-to-remediate.
Approaches to assessment for modern attack surface management must be continuous, not periodic, due to digital infrastructure dynamics.
- Automated Discovery and Monitoring. Continuous ASM programs automate asset discovery across multiple vectors including DNS enumeration, certificate monitoring, cloud service APIs, and network reconnaissance. Organizations implement scheduled and triggered discovery processes that maintain real-time visibility into infrastructure changes.
- Integration with DevOps and Cloud Operations. An effective ASM program should integrate with development and operations workflows to identify new assets as they are deployed. This entails integrating APIs with cloud platforms, integrating CI/CD pipelines, and carrying out infrastructure-as-code scanning to check for new exposures as deployments occur.
- Real-time Alerting and Response. Continuous monitoring alerts security teams when a new exposure is discovered or an existing asset changes configuration. When major exposures requiring rapid response are identified, organizations trigger alerting workflows to notify security teams.
- Automated Risk Assessment. Advanced ASM platforms analyze discovered exposures using vulnerability data, threat intelligence, and business context to provide immediate risk scoring and prioritization.
Best Practices for ASM Implementation
Successful ASM implementation requires strategic planning, stakeholder alignment, and operational excellence across multiple dimensions.
Executive Support and Governance. Successful attack surface management requires strong executive sponsorship and clear governance. This includes defined roles and responsibilities, escalation paths, and resource allocation frameworks that support the program over time
Risk-Based Prioritization. ASM programs implement risk-based methodologies that consider business context, threat landscape, and organizational priorities. Organizations are encouraged to focus remediation efforts on exposures that represent genuine business risk rather than pursuing technical completeness alone.
Comprehensive Asset Coverage. Complete attack surface visibility requires discovery across all organizational domains including on-premises infrastructure, multi-cloud environments, SaaS applications, mobile applications, and third-party services. Organizations maintain accurate, real-time inventories that reflect the full scope of their digital presence.
Tool Integration and Automation. ASM should be integrated with existing security tools, IT service management platforms, and business processes to improve efficiency and consistency. Automation enables faster, more consistent responses while reducing manual effort and allowing security teams to focus on strategic work.
Cross-Functional Collaboration. ASM programs are not limited to security teams. Business stakeholders, system administrators, cloud engineers, and application developers should also be involved. When an exposure is discovered, clear communication protocols support a coordinated response and shared understanding.
Metrics and Continuous Improvement. Organizations establish measurement frameworks that track program effectiveness and drive continuous improvement. Key metrics include mean time to discover new assets, critical vulnerability remediation time, attack surface size trends, and overall risk reduction achievements.
What Challenges Do Modern Organizations Face in Attack Surface Management?
Contemporary ASM programs address multiple complex challenges requiring innovative approaches and strategic thinking.
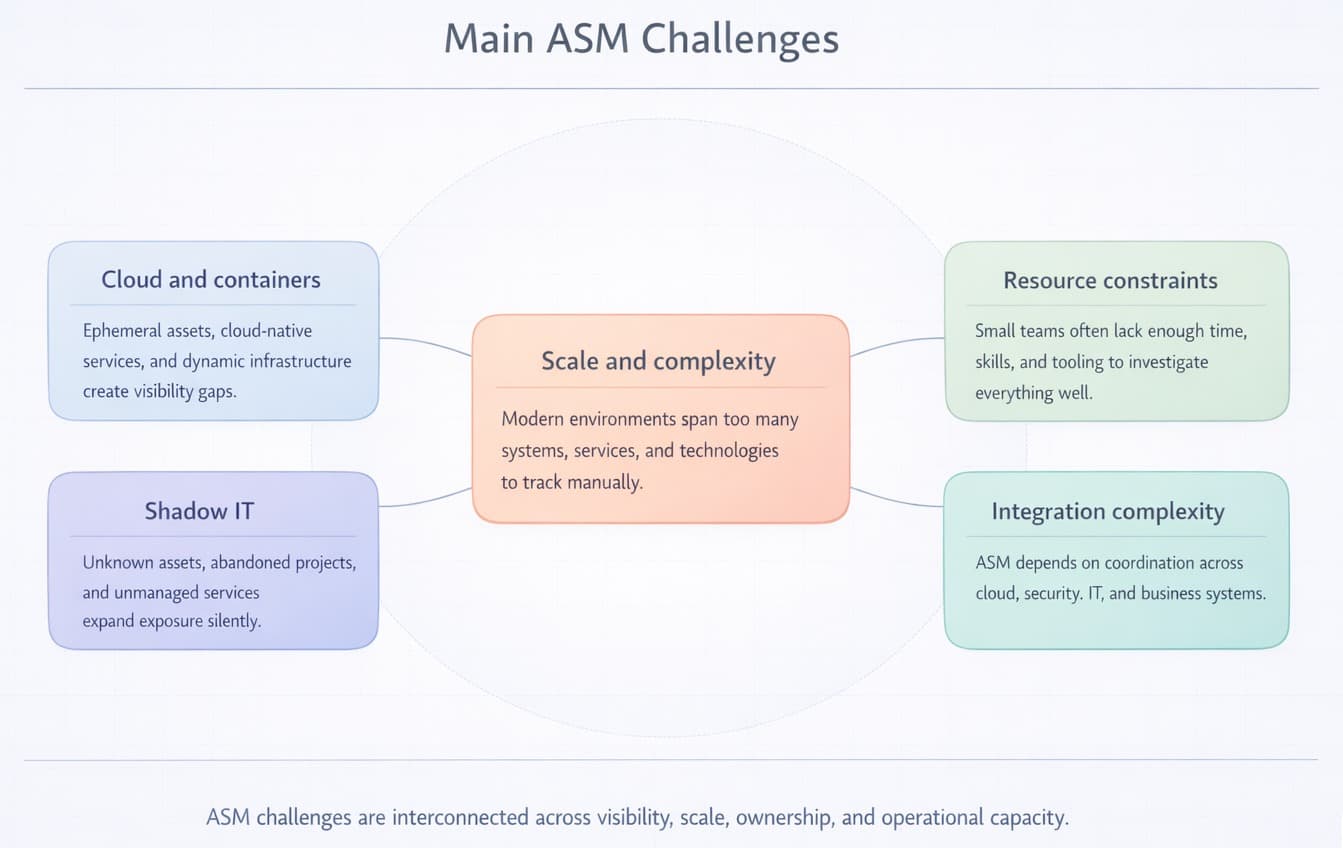
Scale and Complexity
Today’s IT environments are far more complex than traditional networks. Organizations manage on-premises systems, multi-cloud services, mobile devices, IoT infrastructure, and SaaS applications, creating attack surfaces that span multiple domains and technologies.
Cloud and Container Environments
Cloud-native and containerized environments present unique ASM challenges. Traditional discovery techniques prove insufficient for ephemeral resources like containers and serverless functions, requiring specialized tools and methodologies that understand cloud-specific architectures.
Shadow IT and Asset Sprawl
Organizations often discover previously unknown assets during their first ASM baseline, especially across cloud accounts, subsidiaries, expired projects, and third-party services. Shadow IT, abandoned projects, and unmanaged cloud resources create significant blind spots in traditional security approaches.
A good real-world example comes from Cloudflare's 2024 incident write-up: the threat actor gained access using one service token and three service accounts that had not been rotated because they were mistakenly believed to be unused. For readers, this is a strong reminder that forgotten credentials and old integrations are part of the real attack surface too.
Resource and Skill Constraints
Due to constraints related to security personnel, skills and technology, many organizations are not able to implement ASM. Programs should provide broad coverage while accounting for resource constraints and building capabilities over time.
Integration Complexity
ASM calls for integration between cloud, business systems, and multiple security tools. Organizations must manage technical integrations carefully while avoiding unnecessary operational overhead caused by tool sprawl.
The Future of Attack Surface Management
The ASM landscape continues evolving rapidly, driven by technological advancement, changing threat patterns, and organizational digital transformation.
AI and Machine Learning Integration - advanced analytics capabilities enable predictive analysis, automated threat correlation, and intelligent risk assessment. Machine learning algorithms identify attack patterns, predict likely attack vectors, and automate routine discovery and assessment tasks.
Continuous Threat Exposure Management (CTEM) - the evolution toward CTEM represents the next maturity phase, combining attack surface management with continuous validation of security control effectiveness, real-time exposure assessment, and proactive threat hunting capabilities.
Zero Trust Architecture Convergence - ASM provides foundational visibility required for Zero Trust implementation, enabling dynamic trust decisions based on real-time asset and risk assessment. This convergence represents a fundamental shift toward trust verification rather than perimeter-based security models.
Conclusion
Attack surface management is a proactive security practice focused on identifying and reducing exposure before it can be exploited. For modern organizations, this makes ASM an important part of a broader cybersecurity program.
Systematic attack surface management can improve visibility, support prioritization, and help reduce exposure across complex environments. With market growth projections indicating explosive expansion and increasing regulatory focus on exposure management, ASM has evolved from tactical security tool to strategic business capability essential for organizational survival in an interconnected world.
For cybersecurity professionals and IT leaders, the question is no longer whether ASM matters, but how quickly they can build a practical program that improves visibility and reduces exposure.
Five questions to ask after reading this article:
- Do we know every external domain and subdomain we own?
- Which internet-facing assets do not have a clear owner?
- Which public-facing findings are linked to active exploitation evidence?
- What changed in our external attack surface in the last 7 days?
- Which exposed assets could give an attacker identity, admin, or data access first?